

Cyber Security Solutions Built for UK Business Resilience
The New Era of UK Cyber Risk
Securing Your hybrid cloud & Remote Workforce
Board-Level Liability in the Age of NIS2
The Real Cost of a Modern Breach
That's why we prioritise adaptability, beyond just preventing attacks; we always ensure that if an attack does happen, we're able to recover quickly and effectively.
Our Methodology: The Cyber Defence Lifecycle
- Assess & Govern: Quantifying Risk & NCSC Alignment
We start by speaking the language of business, not code. We audit your infrastructure against NCSC frameworks to provide a clear heat map of your vulnerabilities and a strategy to minimise them. - Protect & Fortify: Sovereign, Zero-Trust Architectures
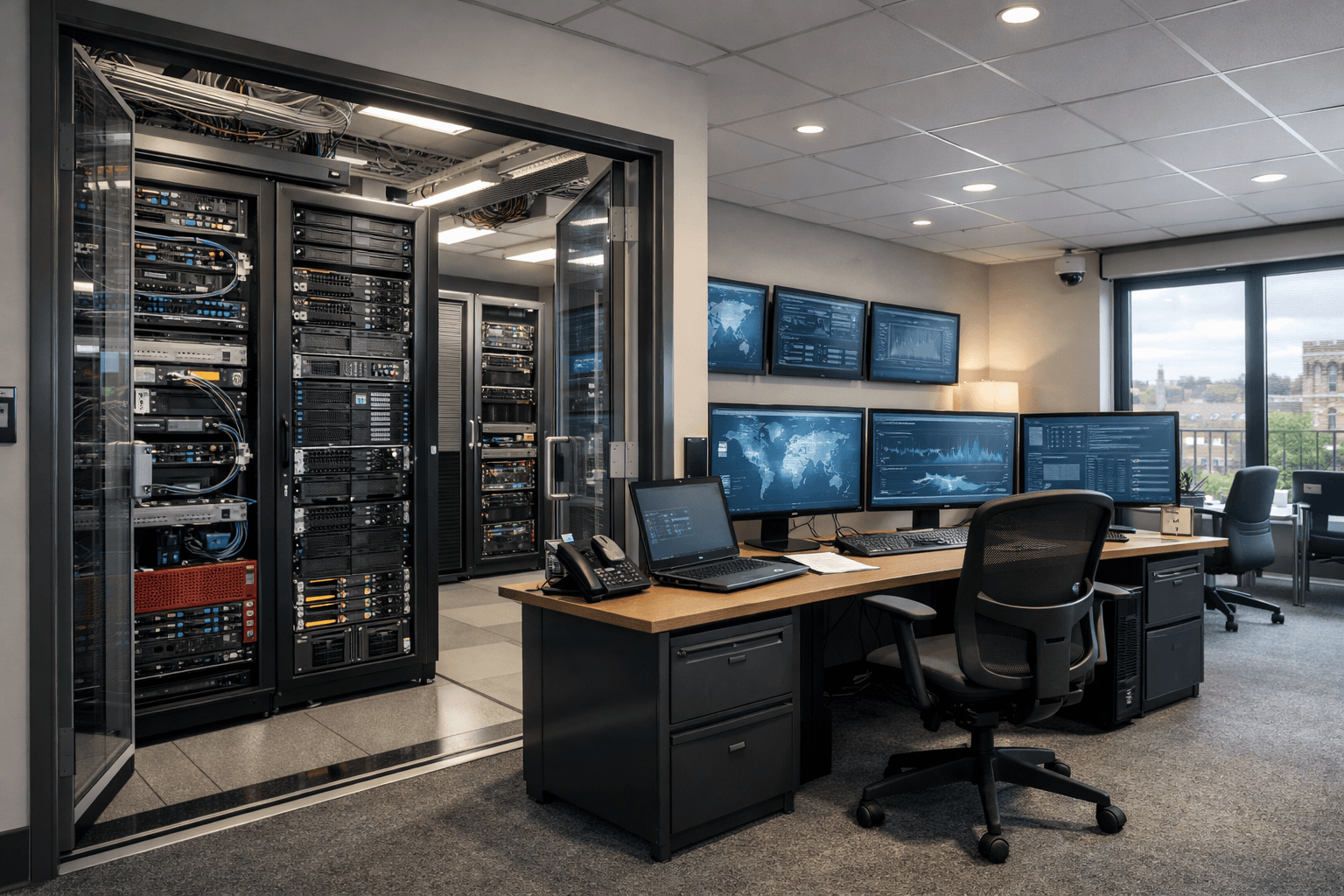
We follow a "never trust, always verify" approach. By implementing sovereign architectures, we make sure that your data stays under UK jurisdiction and is protected by advanced encryption and access controls. - Detect & Respond: 24/7 Active Threat Hunting
Static defences are vulnerable to being bypassed. Our UK-based Security Operations Centre (SOC) provides active threat hunting, identifying and neutralising silent intruders before they can cause damage to your system. - Assure & Evolve: Demonstrating Compliance
We give you the real-time reports and insights that provide clarity and transparency required to showcase your compliance status to stakeholders, insurers, and regulators.
Our Core Cyber Security Solutions
Proactive Threat Management & 24/7 Defence
We provide constant monitoring, incident response, and vulnerability management tailored to the UK time zone and threat profile.
Identity, Access & Infrastructure Security
We use advanced multi-factor authentication (MFA) and identity access management (IAM) to ensure that only authorised users can access your systems.
Cloud Security Posture Management (CSPM)
As you expand in the cloud, even small misconfigurations can pose big risks. We provide essential guardrails for your Azure, AWS, or Hybrid environments, ensuring your cloud security matches that of your on-premise servers.
Risk, Governance & Compliance Programmes
From Cyber Essentials Plus to ISO 27001, we make your certification process simple. We handle the paperwork and technical evidence, so you don’t have to waste your energy staying worried while confidently showing your clients and partners that you take the security aspect seriously.
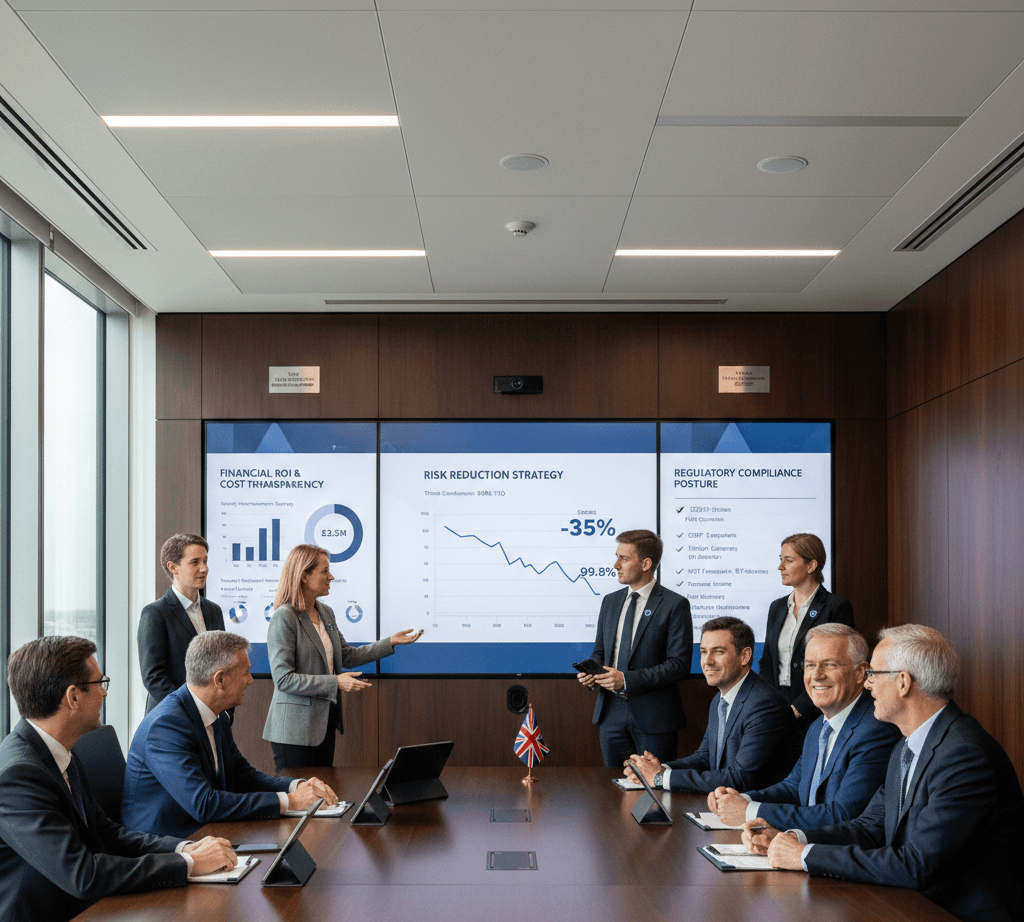
Why Enterprises Choose a Strategic Partner Over a Tool Vendor?
- UK Sovereign Operations: Our security experts are UK-vetted, and our data centres are based in the UK, so we truly understand local regulations and compliance requirements.
- Business-Led Reporting: No technobabble. Just clear reporting on business impact, reduced risk, and ROI, so your board can make informed decisions without facing complexities.
- Commercial Certainty: We offer straightforward, predictable pricing with complete transparency. No unexpected cost or licensing increases, just efficient security and clear visibility on all costs from the outset.
Related Solutions
Security That Enables, Rather Than Inhibits.
In evolving threats, good enough isn't enough. Our team provides a multi-layered defence strategy that protects your data without slowing down your people and operations!